Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

Enforcing Reliable and Protected URL Encoding and Decoding in Java
Ensuring the security and integrity of data is paramount in the dynamic world of software…

Enhancing Cloud Security Like No Other with BrainIAC
In the dynamic landscape of cloud computing, security remains a paramount concern. As organizations increasingly…

Is Artificial Intelligence a Threat to Cybersecurity?
With the growth of technology, AI and cybersecurity have engendered questions about threats that may…
Creating Effective Docker Images with the Help of Container Security
There are times Docker images are created without much thought to security. However, given the…
Can AI Improve Code Security in DevOps? Exploring the Role of AI in Writing Secure Code
DevOps is a set of practices that combines software development and IT operations to enable…
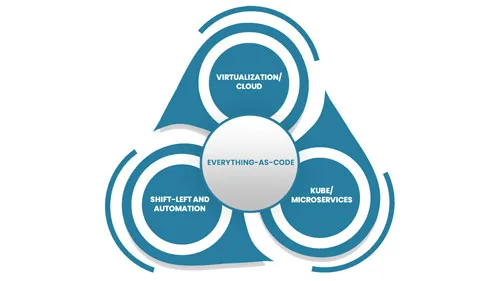
Everything-as-Code
Everything-as-Code (EaC) is the future of IT; the benefits are simply overwhelming. EaC is the…

Continuous Monitoring in Container Security: Safeguarding Your Digital Ecosystem
Security is paramount in the containerized applications landscape, where agility meets complexity. Traditional security measures…

Embracing Zero Trust: A Paradigm Shift in Container Security for Web Applications
Security remains a paramount concern. Traditional security models are often insufficient to combat the sophisticated…

The Importance of SBOMs in Managing IoT Software Security
Building with open-source software is essential for many IoT developers. Open-source software provides a wealth…

Using IaC to Manage Edge Computing Infrastructure
Edge computing is the distribution of computing power and data storage closer to where data…
