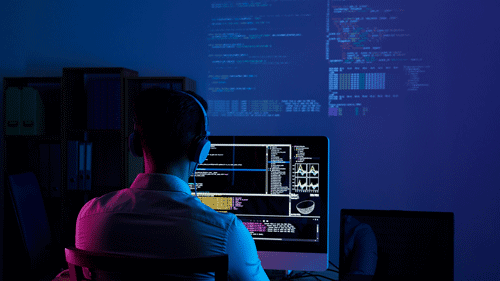
The age of containerization has ushered in a new era of container security: one where there are many open-source tools and services to help you monitor, secure, and optimize your containers. However, the need to scan containers for vulnerabilities is just as important as ever, especially with today's new IT landscape, where developers have more control over the entire DevOps process. Container security threats have become more sophisticated in recent years, with attackers increasingly targeting containerized environments. When your organization takes advantage of the benefits of containers, you must recognize the need to remain vigilant about your container security posture. One important way to do this is by consistently scanning your containers for vulnerabilities.
In today's cloud computing and DevOps world, it's critical to scan your container images for vulnerabilities before and after they are deployed. And this process should be done constantly; here's why.
1. Modern IT infrastructures rely on containers
The modern IT landscape is quickly becoming dominated by containerization as more companies turn to this innovative approach to deploying software and services. The benefits of containerization are numerous; Quick deployment of new applications and services, faster release cycles, and high levels of scalability are just a few advantages containers provide to modern IT infrastructures. If your organization relies on containers or is looking to make the switch, you must prioritize your container security posture. By leveraging tools and services for scanning and vulnerability analysis, you can monitor for vulnerabilities that could put your containers at risk.
2. New threats require constant vigilance
While the benefits of containerization are clear, it also opens your organization up to new security threats. With the increased speed and agility containers provide, attackers can more easily find and exploit vulnerabilities in your organization's infrastructure. To protect against these threats, it's vital to continuously scan your container images for vulnerabilities, whether you're deploying new applications or updating existing ones. By keeping on top of any changes to your application and container images, you can mitigate the risk of a successful attack against your organization.
3. Automated scanning makes security easier
Scanning for vulnerabilities in your containers doesn't have to be difficult or tedious; there are now many automated tools and services that make it easy to scan your container images continuously. Whether you're working with a pre-built container or building your own, there are several options for scanning your containers for vulnerabilities. You must prioritize constant scanning of your applications and services if you're looking to improve your container security posture. By staying on top of any changes to your infrastructure, you can better protect yourself from new threats and attacks.
4. Ensures containers are kept up-to-date with the latest security patching
Keeping your containers up-to-date with the latest security patches is another crucial way to avoid potential threats. By scanning your containers for vulnerabilities and updating them with any necessary patches, you can mitigate the risk of a successful attack on your organization's infrastructure. When it comes to security, it's essential to stay on top of any changes that might affect your infrastructure. Whether deploying a new application or updating an existing one, continuous scanning can help ensure that your containers are kept up-to-date with the latest security patches and measures.
5. Minimizes downtime and disruption to the organization
Lastly, the need for constant scanning is driven by the fact that it can minimize the impact of an attack on your organization. By monitoring for vulnerabilities and mitigating them before they turn into significant issues, you can greatly reduce any downtime or disruption to your services. Regular scanning is a critical part of maintaining a strong container security posture. Whether you're deploying new applications or updating existing ones, continuous scanning can help minimize the impact of potential threats and attacks on your organization. It takes a lot of effort to stay on top of any changes to your infrastructure, but the benefits of regular scanning make it a worthwhile investment.


No Comments Available...